Vulnerability Assessment: Investing "Thousands" to Protect "Millions"

As a business owner, have you ever wondered, "How secure is our IT system?" Often, we set up our systems and continue using them without realizing which "back doors" might have been left unlocked—until a data breach or ransomware attack occurs. The resulting damage is frequently many times higher than the cost of prevention. This is why Vulnerability Assessment (VA) has become an essential tool for modern executives to professionally check their company's security health.
What is a Vulnerability Assessment (VA)?
If you compare your IT system to an "office building," performing a Vulnerability Assessment is like hiring an expert to inspect the entire premises. They check for broken door locks, unlatched windows, or any entry points a thief could use. Afterward, they provide a detailed report so you can "repair" these weaknesses before a threat arrives.
4 Key Benefits for Executives Investing in VA in 2026
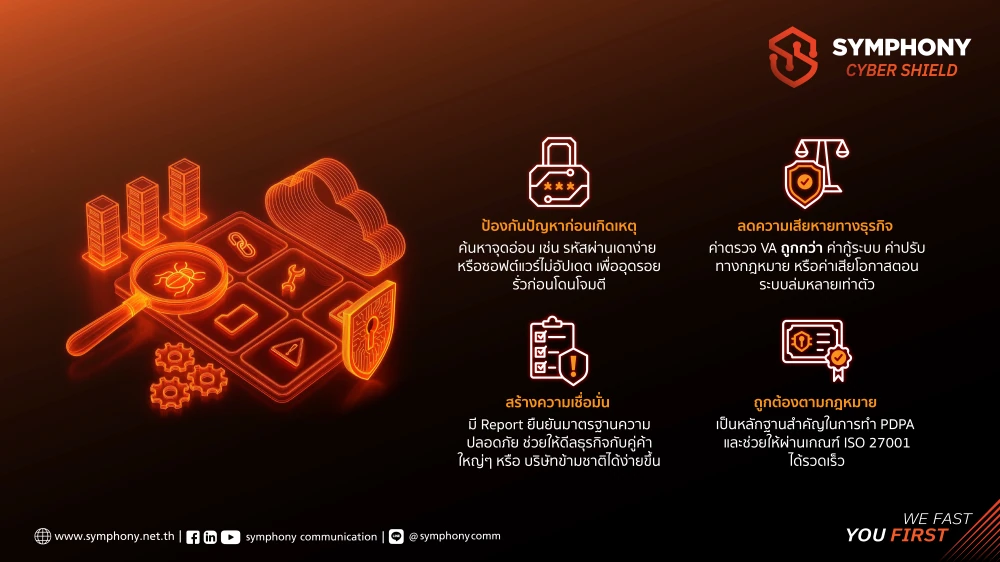
1. Prevention: Identify weaknesses—such as weak passwords or outdated software—before hackers can exploit them. This allows you to plug leaks and ensure Business Continuity without interruptions.
2. Cost-Efficiency: The cost of a VA service is significantly "cheaper" than system recovery fees, legal fines from data leaks, or the loss of revenue during a total system shutdown. It is a safeguard against potential losses in the hundreds of thousands or millions.
3. Business Trust: An up-to-date VA report serves as a certificate of security standards, increasing your chances of securing deals with major partners or multinational corporations.
4. Compliance: It helps your organization quickly adhere to legal requirements and security standards (such as PDPA or ISO 27001).
How Often Should You Check Your IT Health?
To ensure your business remains secure year-round, we recommend performing a VA at these critical times:
- Regularly: Monthly or quarterly (similar to an annual physical check-up).
- During Changes: After installing new software, replacing servers, or major system updates.
- New Threats: If you suspect a risk or encounter new cyber threats in the news.
Don't let your hard work in building a business crumble due to an invisible IT loophole. A Vulnerability Assessment is not a technical burden; it is the most cost-effective risk management strategy to protect your organization's assets and long-term credibility.
